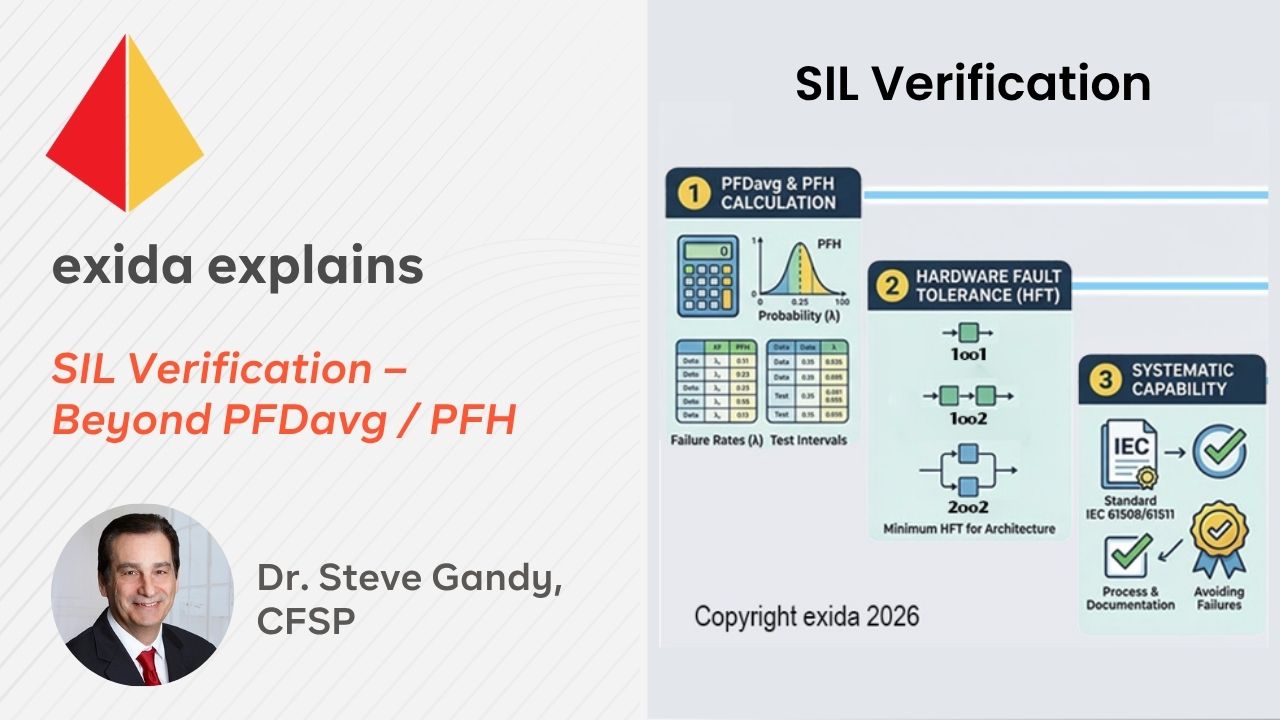
Have you ever heard people say, “I’ve met the PFDavg target, so I’ve met my SIL target?” It’s true that in low demand we need to meet the PFDavg (or PFH for High/Continuous mode)…
exida explains Blog
- by Dr. Steve Gandy, CFSP
- Monday, May 11, 2026
- Functional Safety
SIL Verification - Beyond PFDavg / PFH

- by
- Thursday, April 16, 2026
- Industrial Cybersecurity
Why PLCs Are Not Hardware Security Boxes Under the EU CRA
Introduction
Under the EU Cyber Resilience Act (CRA), product classification drives the compliance path—including the depth of required evidence and whether conformity can be supplier-led or requires third-party involvement. This post explains why programmable…

- by Sarah O'Brien
- Monday, March 30, 2026
- Industrial CybersecuritySoftware
From HLRA to DLRA: Simplifying OT Cyber Risk Assessment with exSILentia® Cyber
As the cybersecurity landscape continually evolves, engineers here at exida are working with organizations looking to achieve and maintain cybersecurity compliance. Tools like exSILentia® Cyber help end users comply with the standards and improve…

- by Alejandro Esparza, CFSE
- Wednesday, March 11, 2026
- Functional Safety
When “Worst-Case” Isn’t Good Enough: Why Your LOPA Might Be Underestimating Risk
When designing a Safety Instrumented Function (SIF), practitioners often encounter a complex scenario: multiple initiating events (independent causes) leading to the same hazardous consequence. While common industry practice is to design for the "worst-case"…

- by Dr. Steve Gandy, CFSP
- Saturday, February 14, 2026
- Functional Safety
Defeating the Swiss Cheese Model: Managing Random and Systematic Failures Across the SIS Lifecycle
How often have you been at conferences where the presenters refer to the “Swiss Cheese Model”? The intent of the model is to convey what happens to the protection layers in Safety Instrumented Systems…

- by Dr. Steve Gandy, CFSP
- Tuesday, November 04, 2025
- Functional Safety
How Does Mission Time, Proof Test Interval and Proof Test Coverage Impact PFDavg?
Oftentimes when this comes up during class it’s clear that there’s a misunderstanding as to how these three variables can impact the PFDavg calculations. Mission Time is defined as the period of time over…

- by Sarah O'Brien
- Thursday, October 23, 2025
- Software
From exSILentia® to SILstat™ – A Seamless Transition
Looking for a way to manage and maintain your operation and maintenance data, but don’t know where to start? Are you already using exSILentia® for your safety lifecycle task needs?
If so, SILstat™ offers…

- by Sarah O'Brien
- Wednesday, October 15, 2025
- Software
Easy to Navigate – The Intuitive Data Structure of SILstat™
While using different safety system management platforms, it is essential to keep system and device data properly arranged between platforms to ensure efficient data management. This can be difficult, but not with SILstat™.…

- by Dr. Steve Gandy, CFSP
- Monday, September 08, 2025
- Functional Safety
How Does A SIF Achieve its SIL Target?
This is a question I’ve been asked many times, with some stating that as long as the PFDavg (or PFH) meets the target SIL then that’s fine. Whereas this statement is partially true, it…

- by Sarah O'Brien
- Thursday, August 28, 2025
- Software
The Future of Safety Management: Embracing Digital O&M Data
In today’s world, having your Operation and Maintenance (O&M) data in a digital format allows for increased accessibility and traceability. Using more traditional recordings, such as on paper or with various Excel notebooks, increases…

- by Hrishit Joshi
- Tuesday, August 26, 2025
- Industrial Cybersecurity
How IEC 62443 Can Help Achieve Compliance with the EU Cyber Resilience Act (CRA)
Introduction:
The European Union’s Cyber Resilience Act (CRA) is set to introduce mandatory cybersecurity requirements for “products with digital elements”, including those used in Industrial Control Systems (ICS) and Operational Technology (OT) environments. This…

- by Alejandro Esparza, CFSE
- Friday, August 08, 2025
- Functional Safety
Más allá de la baja demanda: Entendiendo el verdadero modo de operación de tu SIF (Beyond Low Demand: Understanding Your SIF’s True Mode of Operation)
ESPANOL
¿Se calcula el SIL de una SIF de Demanda Baja igual que el de una SIF de Demanda Alta o Continua?
Es muy importante identificar el modo de operación que es asignado a…

- by Hrishit Joshi
- Monday, July 28, 2025
- Industrial Cybersecurity
Understanding the EU Cyber Resilience Act (CRA)
Introduction:
The European Union Cyber Resilience Act (CRA) is a landmark regulation designed to enhance cybersecurity across hardware and software with digital elements that are offered for sale within the EU. As cyber threats…

- by Dr. Steve Gandy, CFSP
- Tuesday, July 08, 2025
- CertificationFunctional Safety
What Does IEC 61511 Mean by Competency?
When the latest edition of IEC61511 was published in 2016, one of the key changes was the emphasis on competency and some further guidance on what this means. The relevant clauses in the IEC61511:2016…

- by Valerie Motto
- Monday, June 16, 2025
- Functional Safety
A Component Reliability Data Source Must Include Useful Life
In exida’s Component Reliability Database (CRD), every component includes a Useful Life expressed in years and/or cycles.
Understanding Useful Life
This post, drawing from exida's whitepaper [1] on how environmental factors impact component…
exida explains
The exida explains blog gives expert and sometimes candid insight into the world functional safety, alarm management, and industrial cybersecurity.
