An insider’s view…
Written By: Mike Medoff, Co-chair of JT 62443-4-1
The clock is ticking for manufacturers selling products with digital elements into the European Union. By December 2027, compliance with the Cyber Resilience…

Written By: Mike Medoff, Co-chair of JT 62443-4-1
The clock is ticking for manufacturers selling products with digital elements into the European Union. By December 2027, compliance with the Cyber Resilience…
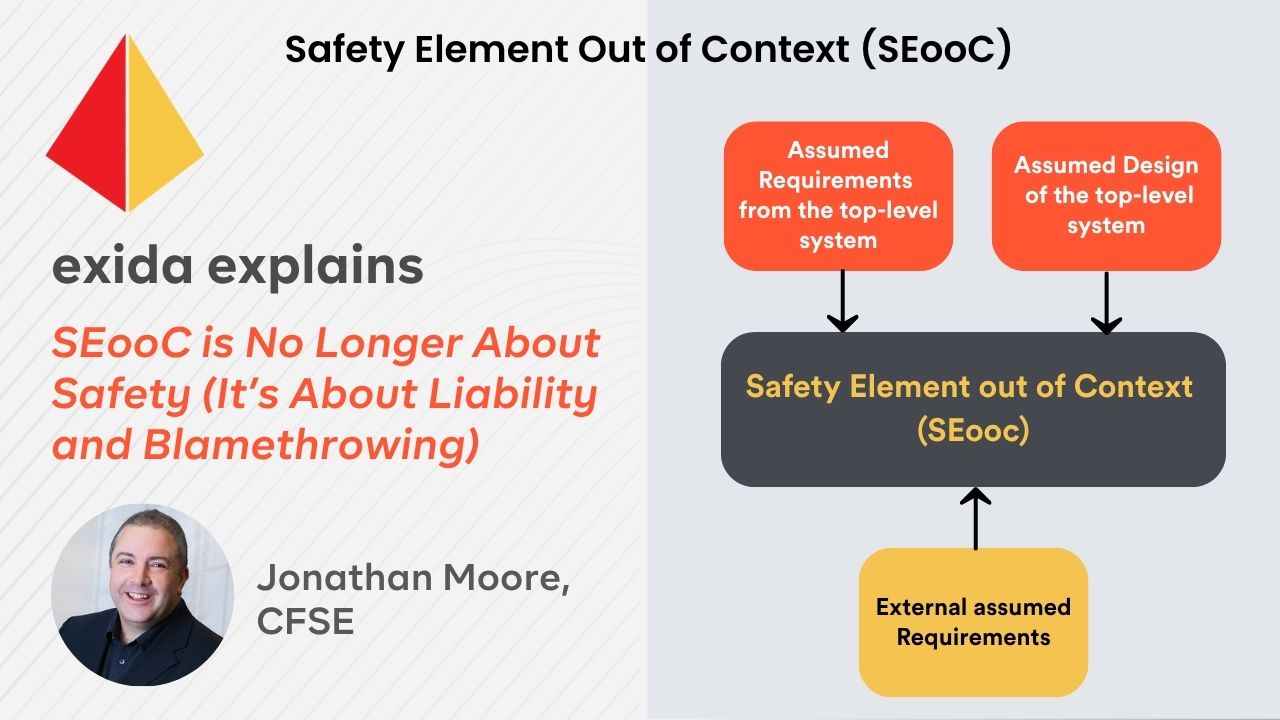
I've worked in automotive all my life. I had the lucky chance to work for a large Tier 1 supplier of test and engineering services that happened to also act as the project manager…
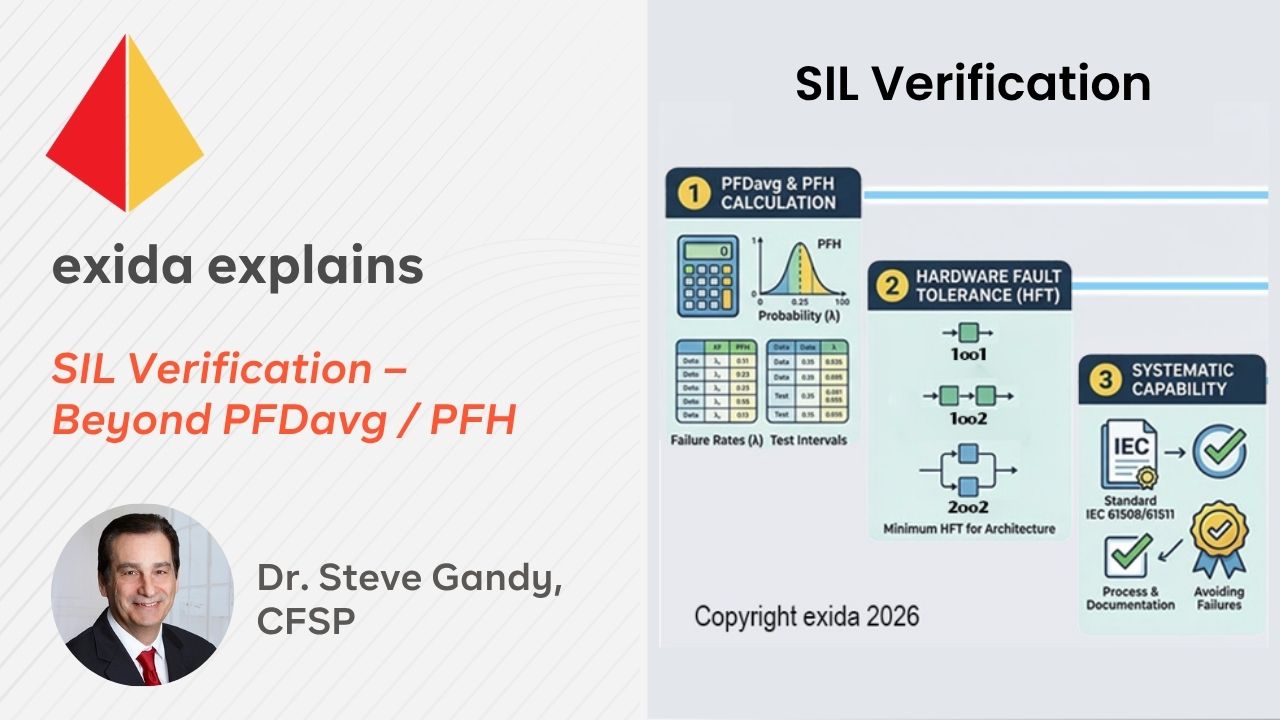
Have you ever heard people say, “I’ve met the PFDavg target, so I’ve met my SIL target?” It’s true that in low demand we need to meet the PFDavg (or PFH for High/Continuous mode)…

Under the EU Cyber Resilience Act (CRA), product classification drives the compliance path—including the depth of required evidence and whether conformity can be supplier-led or requires third-party involvement. This post explains why programmable…

As the cybersecurity landscape continually evolves, engineers here at exida are working with organizations looking to achieve and maintain cybersecurity compliance. Tools like exSILentia® Cyber help end users comply with the standards and improve…

When designing a Safety Instrumented Function (SIF), practitioners often encounter a complex scenario: multiple initiating events (independent causes) leading to the same hazardous consequence. While common industry practice is to design for the "worst-case"…

How often have you been at conferences where the presenters refer to the “Swiss Cheese Model”? The intent of the model is to convey what happens to the protection layers in Safety Instrumented Systems…

Oftentimes when this comes up during class it’s clear that there’s a misunderstanding as to how these three variables can impact the PFDavg calculations. Mission Time is defined as the period of time over…

Looking for a way to manage and maintain your operation and maintenance data, but don’t know where to start? Are you already using exSILentia® for your safety lifecycle task needs?
If so, SILstat™ offers…

While using different safety system management platforms, it is essential to keep system and device data properly arranged between platforms to ensure efficient data management. This can be difficult, but not with SILstat™.…

This is a question I’ve been asked many times, with some stating that as long as the PFDavg (or PFH) meets the target SIL then that’s fine. Whereas this statement is partially true, it…

In today’s world, having your Operation and Maintenance (O&M) data in a digital format allows for increased accessibility and traceability. Using more traditional recordings, such as on paper or with various Excel notebooks, increases…

The European Union’s Cyber Resilience Act (CRA) is set to introduce mandatory cybersecurity requirements for “products with digital elements”, including those used in Industrial Control Systems (ICS) and Operational Technology (OT) environments. This…

¿Se calcula el SIL de una SIF de Demanda Baja igual que el de una SIF de Demanda Alta o Continua?
Es muy importante identificar el modo de operación que es asignado a…

The European Union Cyber Resilience Act (CRA) is a landmark regulation designed to enhance cybersecurity across hardware and software with digital elements that are offered for sale within the EU. As cyber threats…
The exida explains blog gives expert and sometimes candid insight into the world functional safety, alarm management, and industrial cybersecurity.
